Nitrokod, a Turkish-speaking entity, has been linked to an ongoing cryptocurrency mining campaign that involves imitating a desktop application for Google Translate in order to infect over 111,000 victims in 11 countries since 2019.
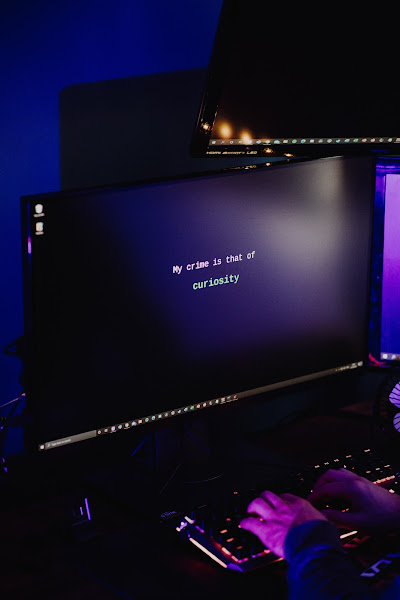
Maya Horowitz, vice president of research at Check Point, said in a statement shared with The Hacker News, “The malicious tools can be used by anyone. They can be found by a simple web search, downloaded from a link, and installation is a simple double-click.”
The victims come from the United Kingdom, the United States, Sri Lanka, Greece, Israel, Germany, Turkey, Cyprus, Australia, Mongolia, and Poland. The campaign involves the distribution of malware via free software hosted on popular websites such as Softpedia and Uptodown.
To evade detection, the malware postpones execution for weeks and distinguishes its malicious activity from the downloaded fake software. Following the installation of the infected program, an update executable is deployed to the disc, launching a four-stage attack sequence with each dropper paving for the next, until the actual malware is dropped in the seventh stage.
When the malware is executed, a connection is established to a remote command-and-control (C2) server to retrieve a configuration file to begin the coin min
[…]
Content was cut in order to protect the source.Please visit the source for the rest of the article.
[…]
Content was cut in order to protect the source.Please visit the source for the rest of the article.
This article has been indexed from CySecurity News – Latest Information Security and Hacking Incidents
Read the original article: